Table of Contents
Every major enterprise follows the same security playbook:
Hire a cybersecurity firm, pay for a multi-month penetration testing engagement, receive a report, ship patches, and repeat next year.
That model worked just fine when attacks followed human timelines, which meant a breach required a skilled individual to probe a target manually over days or weeks. But things have changed. Human activity now accounts for only a minority of online interactions, and the gap between humans and bots is widening every day.
It's a completely different ballgame. AI agents generate novel exploits continuously, testing variations at machine speed and adapting in real time to whatever defenses they encounter, so by the time a traditional firm delivers its findings, the threat profile has already shifted, and the detection logic in that report is obsolete. More budget doesn't solve this problem; a structural upgrade to defense is needed that updates continuously and runs at machine speed.
That's where RedTeam comes in.
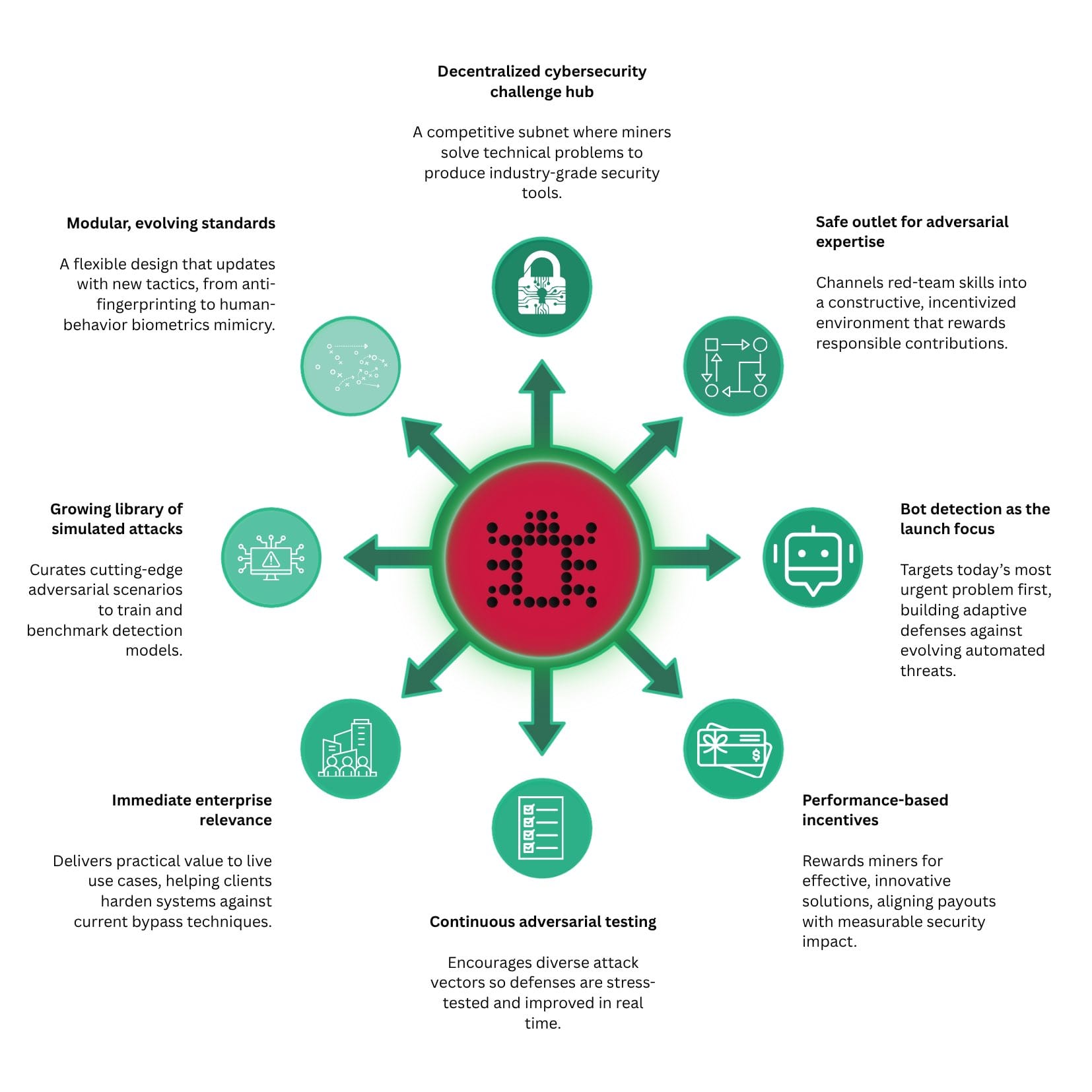
What SN61 Actually Builds
RedTeam is a Bittensor subnet that turns cybersecurity research into a live, continuous, competitive market where miners build, test, and submit security tools that solve active challenges posted by the subnet, and those solutions feed directly into the Innerworks (the commercial arm of RedTeam) production stack.
The subnet’s modular architecture lets challenges be added or removed based on demand. The long-term ambition, as the RedTeam whitepaper frames it, is that RedTeam becomes a general framework for individuals and enterprises to post bounties solved through Bittensor, with results that improve continuously as the miner network keeps competing.
Two challenges are active right now:
- Auto Browser Sniffer (AB Sniffer): Miners build SDKs that detect and identify automation frameworks by name, across both headless and headed-but-silent browser modes. Per the RedTeam project update, AB Sniffer v1 produced 4 accepted commits and v4 produced 105, a 26x increase driven entirely by competitive incentive.
- Anti-Detect Automation Detection (AAD): Miners detect browser automation running inside anti-detect browsers where static fingerprint signals are masked, and fingerprints are freshly generated on each session, relying entirely on runtime behavior and orchestration patterns rather than static signals.
The subnet has run 14 total challenges since launch and deprecated 9. When miners converge on fully solving a challenge, it ends, and a harder one begins. The difficulty ceiling rises by design, keeping the research output ahead of what attackers deploy.
The Incentive Design That Keeps Research Current
RedTeam's scoring system rewards performance and diversity simultaneously. This dual structure makes the subnet’s research library more valuable than the output of any centralized team.
Performance points go to miners whose solutions improve on the previous best submission, creating direct pressure to keep advancing. Meanwhile, diversity points reward solutions that differ meaningfully from all existing approaches. Because a library of varied attack methods produces more robust defenses than incremental refinements on a single technique, the incentive design deliberately resists monoculture.
Points decay on a linear schedule, so a strong submission from two weeks ago earns progressively less of the emission pool, which means maintaining reward share requires continuous improvement rather than a single breakout submission.
All submissions are encrypted at the time of submission, with the decryption key released after 24 hours, preventing other miners from copying before the originator receives credit, while establishing a clear timestamped record. Solutions are then evaluated in sandboxed environments on secure external servers, so scoring is consistent and can’t be gamed.
Turns out bot protection is an incentive mechanism also https://t.co/hXwSJsV26Q
— const (@const_reborn) February 13, 2026
Three roles operate on the subnet:
- Miners submit solutions and compete for TAO rewards based on performance and diversity scores.
- Validators hold TAO stake, score submissions, and earn rewards proportional to how closely their scores align with network consensus, incentivizing accurate evaluation.
- Subnet owners maintain the infrastructure and earn rewards based on how valuable validators find their subnet relative to others across the Bittensor network.
The roadmap adds a fourth commercial layer: validators will acquire enterprise clients through a frontend web application proportional to their delegated TAO stake. They will also charge fees based on challenge complexity and duration, and give enterprise clients security solutions that continuously improve over time instead a one-time report, turning validators into a direct commercial interface between enterprises and the decentralized network.
1inch Is Already a Paying Customer
A subnet that produces research without a commercial deployment path is an academic exercise.
Innerworks is the RedTeam commercial arm that takes what SN61 miners produce and deploys it at enterprise scale. The two are structurally interdependent; without the subnet, Innerworks loses the continuously-updating R&D advantage that separates it from every other cybersecurity vendor. Without Innerworks, the subnet’s outputs don't generate a commercial return.
The confirmed production deployments are:
- A major global messaging platform and its full ecosystem, running device intelligence, bot detection, and true geolocation across more than 100 million daily active users. Full public details are forthcoming; the team confirms this is live production, not a pilot.
- 1inch, a leading DeFi protocol, is a confirmed paying customer serving 25 million users with over $500 million in daily transactions, confirmed by the 1inch blog. Innerworks integrates device fingerprinting, bot detection, and geolocation intelligence directly into 1inch’s defense systems, with both companies building a predictive AI-powered immune system designed to anticipate and neutralize threats before they reach users.
“Hackers are no longer just human. They’re synthetic, powered by AI, and capable of breaching every mainstream solution. RedTeam proves this with a 99% bypass rate. By partnering with 1inch, we’re converting this intelligence into a collective immune system that defends crypto, and eventually, the wider internet.” — Oli Quie, CEO, Innerworks
That 99% bypass rate means the research SN61 miners produce defeats existing mainstream defenses almost universally.
Beyond the two confirmed deployments, Innerworks is in active integration or proof-of-concept with DEXs, transaction monitoring platforms, payment providers, and identity verification tools.
Four Scoring Iterations and What Each One Fixed
The subnet launched at v1 and is now at v4.0.0, a full restructuring from a tightly coupled monorepo into modular, dedicated repositories for validators, miners, and the scoring server. The project maintains 46 repositories, over 2,000 commits, and 26 releases shipped across the v1-to-v4 cycle.
Validators require a GPU with at least 24 GB vRAM, enabling LLM inference for challenges that require it. Miners submit using standard CPU servers, though GPU access may be needed for local testing on computationally intensive challenges.
The scoring system reached its current form after four distinct iterations, each addressing the failure mode of the version before it:
- Winner-takes-all: rewarded only the top submission per cycle, making participation economically irrational for anyone outside first place and killing retention.
- Softmax-based distribution: spread rewards proportionally across multiple miners, solving retention but creating insufficient pressure for continuous improvement.
- Time-based decay with stability windows: gave submissions full rewards for 10 days, progressive decay through day 15, and full expiration after, requiring miners to beat their own previous best to maintain share.
- Current system: adds filtering, similarity penalties, and de-duplication on top of decay, preventing gaming across multiple UIDs and penalizing submissions that copy existing approaches without advancing them.
Each iteration produced measurably better submission quality. Early miners obfuscated code and attempted to bypass challenges rather than solve them, and after validation pipelines, ESLint checks, and minimum scoring thresholds were introduced, that changed sharply.
A centralized scoring server handles all validation and comparison across the network, preventing weight divergence among validators and reducing redundant compute costs.
On the roadmap: an abstracted mining interface built like Kaggle, where miners sign in with social accounts and bypass wallet complexity entirely, lowering the barrier for security researchers who don’t want to manage on-chain infrastructure.
Why Buybacks Flow to Miners, Not a Centralized R&D Team
Most crypto projects raise capital, build an internal team, and route the R&D budget into that centralized operation, leaving token holders downstream of all commercial activity. Innerworks routed the budget differently.
Miners are the R&D department on SN61, and the R&D budget goes to them. The current commitment is a baseline of 1 TAO per day in Alpha buybacks from Innerworks’ operating budget, running now, with the team explicitly calling it a floor rather than a ceiling: as commercial milestones are reached, additional buybacks are committed, and the overall allocation grows as Innerworks scales.
Innerworks carries significant operating expenditure that’s never been subsidized by the subnet or its emissions, which means the buyback model runs entirely from commercial revenue rather than token inflation.
As Innerworks grows toward the R&D budget of a full-scale enterprise security product, those expenses flow through the subnet rather than into a closed internal team, giving miners the economics of a company's R&D budget as the product scales.
It's a direct revenue loop already in motion:
- Miners submit attack tools
- The subnet evaluates and validates submissions
- Validated outputs feed into Innerworks’ production stack
- Innerworks uses this continuously updated research to win enterprise contracts
- Contract revenue flows back into the network through buybacks and increased rewards
- Stronger incentives attract more skilled miners
- Better miners produce higher-quality research, improving future contract outcomes
Each contract reinforces the loop by funding more competition, allowing the advantage over traditional firms to compound with scale.
The Immune System Architecture
The most important thing RedTeam is building is an architecture for how defenses get generated and deployed at machine speed.
The team has already built an internal immune system agent: the system analyzes attacks coming through the subnet, reverse-engineers the methods, generates countermeasures, and presents them to engineers for review. Work that previously required weeks of manual reverse engineering now takes hours.
The next phase removes the human review step entirely. Miners will be incentivized to build adaptive attack agents, tools that continuously evolve their approach until they bypass the active challenge, rather than submitting static scripts. The immune system agent analyzes those attacks in real time, generates defenses, deploys them back into production, and the adaptive agents immediately test against the new defenses, with the cycle running entirely on machine time.
1inch co-founder Sergej Kunz described the goal in the October 27, 2025 partnership announcement: anticipate attacker movements and proactively adapt defenses before threats reach users, which is the immune system model already running in production against 1inch’s 25 million users.
Defense That Doesn’t Expire
Cybersecurity is shifting from periodic analysis to continuous adaptation.
RedTeam reflects that shift in structure, not messaging. Instead of producing reports that age the moment they are delivered, it builds a system where research, deployment, and defense evolve in parallel, driven by open competition and aligned incentives.
What emerges is not simply a better penetration testing workflow, but a different model entirely: one where enterprise security improves as a function of network activity, where R&D scales with demand, and where every new contract strengthens the underlying system rather than resetting it.
If attackers now operate at machine speed, defense must do the same. RedTeam is one of the first attempts to build that reality into production infrastructure.
Disclaimer: This article is for informational purposes only and does not constitute financial, investment, or trading advice. The information provided should not be interpreted as an endorsement of any digital asset, security, or investment strategy. Readers should conduct their own research and consult with a licensed financial professional before making any investment decisions. The publisher and its contributors are not responsible for any losses that may arise from reliance on the information presented.